Google Dorking, also known as Google hacking, is a method for refining search queries to uncover sensitive information or vulnerabilities. By utilizing specific search operators such as site:, filetype:, and intitle:, users can pinpoint data not typically accessible through standard searches. This technique is commonly employed by researchers, security professionals, and hackers alike to find…
Fundamentals of Reverse Engineering
Reverse engineering is vital in cybersecurity, crucial for understanding and countering malicious software and vulnerabilities. Security professionals dissect malware to gain insights into its functionality, intentions, and potential impact on systems, enabling the development of effective countermeasures. Additionally, it reveals hidden features and exploits within software, bolstering defense mechanisms. However, it isn’t solely defensive; attackers…
Attackers Employ Microsoft Graph API to Evade Detection
In a recent report dated May 2, Symantec researchers revealed a concerning trend: attackers are increasingly turning to the Microsoft Graph API, a tool commonly used by developers to access resources on Microsoft cloud services, as a means to fly under the radar of detection systems. The attractiveness of Graph API to malicious actors stems…
The OSI Model: Understanding the Layers of Computer Networks
Two commonly used models in computer networking are the OSI Reference Model and the IP/TCP Model. Within these models, data transfer follows a systematic order known as layer ordering. These layers are responsible for facilitating the transmission of data to its intended destination. Each layer is assigned specific tasks, making it easier to troubleshoot transmission…
Passkeys Now Safeguard Over 400 Million Accounts, Google Reports
It was announced that Google Account users used passkeys for authentication more than 1 billion times, but according to the report, it seems that passwords will remain in our lives for a while longer. What is Passkey and How Works? Passkeys comprise two cryptographic keys: a public key, registered with the online service or app,…
Malware Analysis: A Malicious Javascript Code
The “javascript-malware-collection” repository on GitHub serves as a repository for various forms of malicious code, each capable of compromising systems and stealing sensitive information. Within this repository, we can analyze characteristics of JavaScript-based malicious codes, revealing their intricate functionalities and potential impacts. In this brief static malware analysis, our focus is on examining a specific…
CISA Warns of Ongoing Exploitation of Serious GitLab Password Reset Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has elevated a critical flaw affecting GitLab to its Known Exploited Vulnerabilities (KEV) catalog due to its ongoing exploitation in live environments. Identified as CVE-2023-7028 (CVSS score: 10.0), this high-severity vulnerability could facilitate unauthorized account access through the manipulation of password reset emails, targeting unverified email addresses….
Red Teaming Methodology: Strategies & Approaches
Red teaming is a structured and systematic approach to testing systems, policies, and procedures by simulating real-world attacks or challenges from an adversary’s perspective. This article describes the strategic approach to effectively testing systems, focusing on the methodology behind red team simulations. Planning The initial phase of red teaming entails meticulous planning to delineate objectives,…
Ukrainian REvil Hacker Sentenced to 13 Years
An affiliate of the REvil ransomware group, Yaroslav Vasinskyi, known as Rabotnik, received a 13-year and seven-month prison sentence from a US court. This ruling followed his conviction for orchestrating over 2500 ransomware attacks, demanding a staggering $700 million in ransom payments, and inflicting significant damage on protected computers. Vasinskyi’s modus operandi involved hacking into…
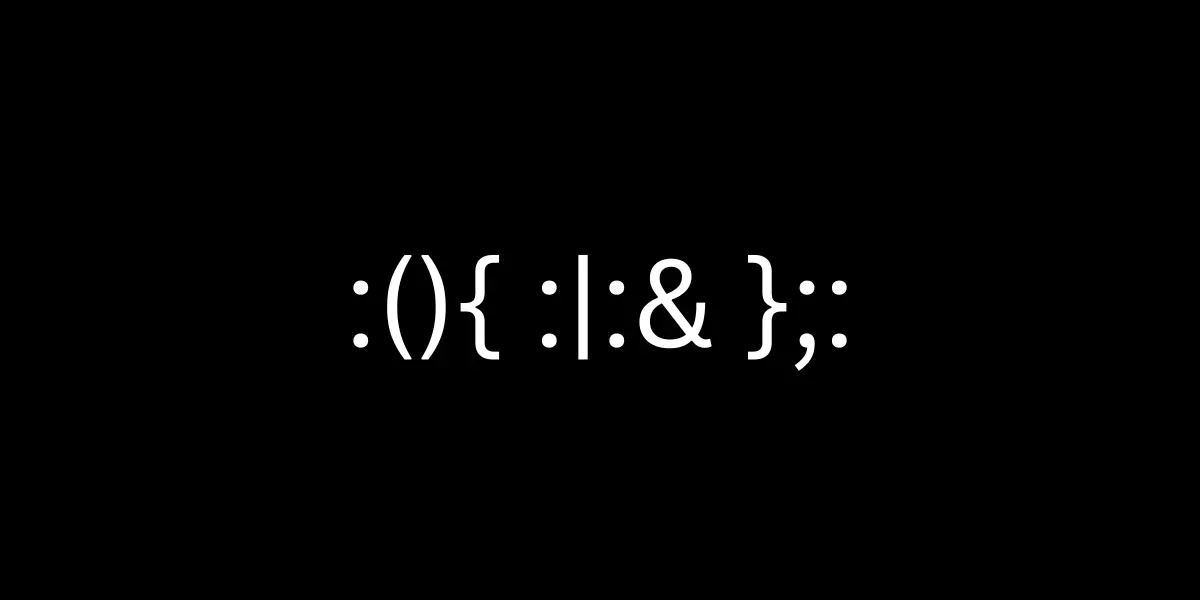
Bash Fork Bomb: A Denial-of-Service Attack
The fork bomb is a potent form of denial-of-service (DoS) assault, specifically targeting Linux or Unix-based systems by leveraging the fork operation. The seemingly innocuous syntax :(){ :|:& };: conceals a devastating Bash function. Upon execution, this intricate code recursively spawns processes, rapidly overwhelming system resources and leading to system crashes. Simplified Fork Bomb Syntax…