Security researchers recently uncovered a new cross-platform malware named Noodle RAT.
Noodle RAT: A New Malware Family
Trend Micro’s security expert Hara Hiroaki has identified Noodle RAT as a significant departure from known malware variants like Gh0st RAT and Rekoobe. Hiroaki explains, “this backdoor represents a new category of malware, rather than just a variant of existing threats.”
Active since at least July 2016, threat actors have deployed Noodle RAT in both Windows and Linux environments.
The malware Gh0st RAT, which surfaced in 2008, marks the earlier phase of Noodle RAT’s evolution. A Chinese group called the C. Rufus Security Team made Gh0st RAT’s source code publicly available. Over time, Chinese state-backed cyber groups have associated themselves with Gh0st RAT and other tools like PlugX and ShadowPad, using them in numerous malicious campaigns.
Hacking groups such as Iron Tiger and Calypso have used the Windows variant of Noodle RAT, which functions as an in-memory modular backdoor. This malware operates through a loader, enabling functionalities such as file downloads/uploads, additional malware deployment, TCP proxying, and self-deletion. Different loaders, such as MULTIDROP and MICROLOAD, have appeared in attacks targeting Thailand and India.
Noodle RAT’s Linux Variant
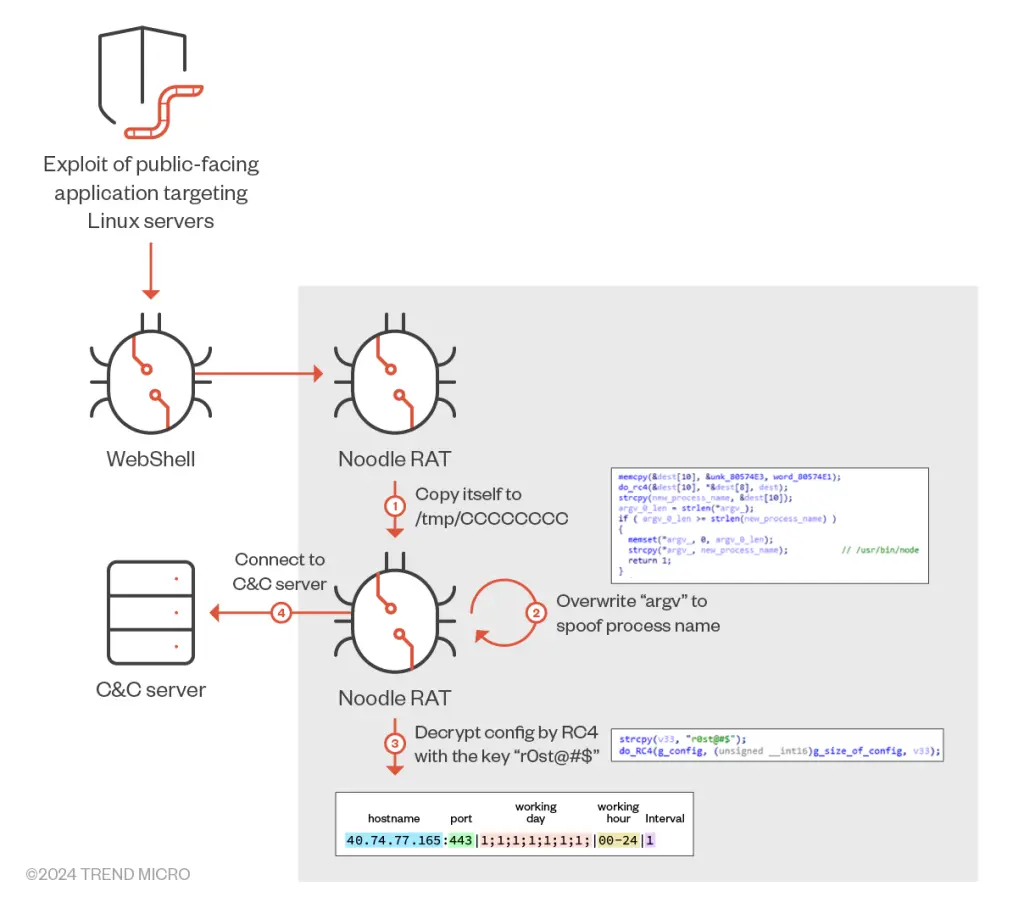
On the Linux side, Noodle RAT has ties to Chinese-linked cybercrime and espionage groups, including Rocke and Cloud Snooper. This malware supports reverse shells, file transfers, task scheduling, and SOCKS tunneling. These attacks typically exploit vulnerabilities in public-facing applications to breach Linux servers, where a web shell provides remote access and enables malware distribution.
Despite differences in their backdoor commands, both the Windows and Linux versions share similar command-and-control (C2) communication methods and configuration formats. Further analysis reveals that while Noodle RAT reuses plugins from Gh0st RAT and has code similarities with Rekoobe, it is fundamentally a new and unique malware strain.
Trend Micro’s investigations revealed the control panel and builder for Noodle RAT’s Linux variant. The associated documentation, written in Simplified Chinese, details bug fixes and enhancements, indicating ongoing development and maintenance. This supports the notion that Noodle RAT is part of a sophisticated supply chain and is sold or distributed among Chinese-speaking entities.
Implications and Threat Landscape
These findings align with the I-Soon leaks from earlier this year, which exposed a broad corporate hack-for-hire ecosystem in China, revealing operational ties between private companies and state-sponsored cyber activities. These tools are likely part of a complex supply chain within China’s cyber espionage framework, marketed to both private and governmental entities involved in state-sponsored operations.
Hiroaki noted, “Noodle RAT is likely shared or sold among Chinese-speaking groups,” highlighting the malware’s historical misclassification and underestimation.
This discovery coincides with reports of Mustang Panda (also known as Fireant), a China-linked group conducting spear-phishing campaigns targeting Vietnamese entities. These campaigns use tax- and education-themed lures to deliver malicious Windows Shortcut (LNK) files, potentially deploying PlugX malware.