The fork bomb is a potent form of denial-of-service (DoS) assault, specifically targeting Linux or Unix-based systems by leveraging the fork operation.
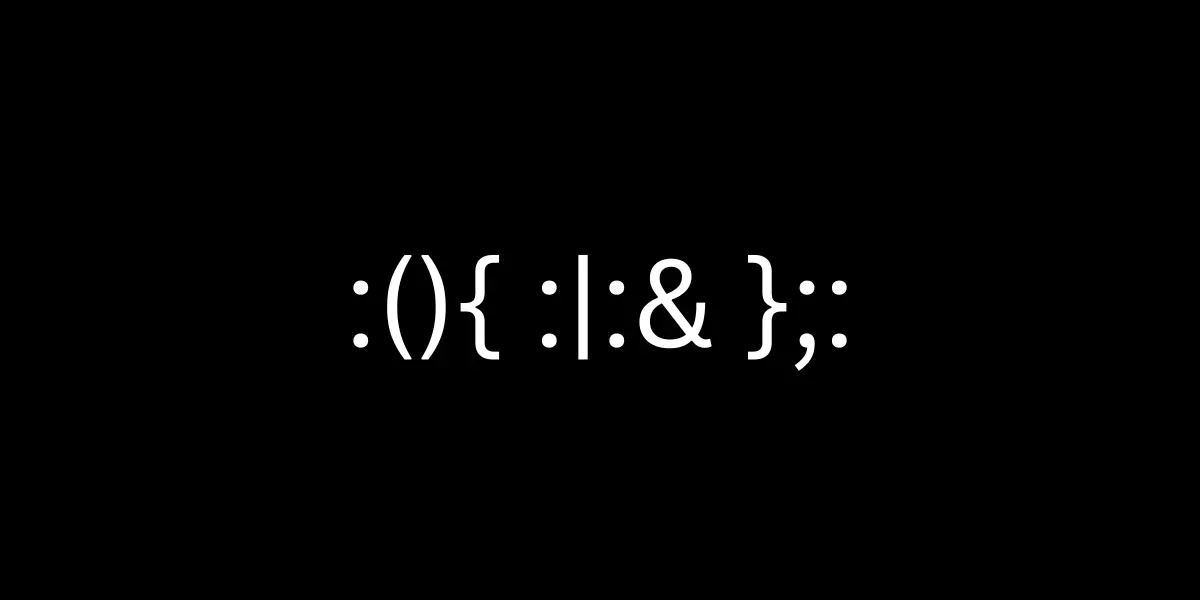
The seemingly innocuous syntax :(){ :|:& };: conceals a devastating Bash function. Upon execution, this intricate code recursively spawns processes, rapidly overwhelming system resources and leading to system crashes.
Simplified Fork Bomb Syntax
:()
{
# code
}When observing code structured in this manner, it becomes apparent that it represents a basic empty function identified solely by a colon.
Initially, its simplicity might evade notice due to the concise single-line syntax characteristic of a fork bomb.
:()
{
:|:&
};:The :|: initiates a recursive loop by calling itself. This means the function keeps calling itself repeatedly, creating a loop (function get called twice).
& – The function call is executed in the background, ensuring that the child process remains active indefinitely, without any chance of termination.
; – Terminate the function definition.
: – Used to call the function.
How Attackers Inject Fork Bombs into Systems
Attackers can deploy system bombs through various vectors, exploiting vulnerabilities in software or leveraging social engineering tactics.
Common methods include malicious email attachments, deceptive website downloads, and compromised network services.
Once inside a system, attackers execute scripts or programs designed to replicate themselves endlessly, consuming system resources and causing denial-of-service (DoS) conditions.
Vigilance against suspicious activities and regular system updates are critical defenses against such attacks.
Preventing Fork Bomb Attacks on Linux
It is possible to take precautions against fork bomb attacks with the help of the ‘ulimit’ command in Linux.
By setting limits on various system resources such as the maximum number of processes a user can spawn, ‘ulimit’ can mitigate the impact of a fork bomb.
Setting appropriate limits helps prevent a single user or process from overwhelming system resources and causing a system-wide slowdown or crash.
ulimit -S -u 5500However, it’s crucial not to set ‘ulimit’ values excessively low, as this could inadvertently restrict system functionality.
Check out more articles about cyber security.