Welcome to our guide on networking basics and simple network attacks. Whether you’re a computer scientist, an ethical hacker, or simply curious about IT, this guide provides a comprehensive introduction.
Understanding Computer Networks
Computer networks refer to the intricate structure formed by connecting various technological devices. These devices span a wide range of technologies, from smartphones and computers to smart refrigerators and light bulbs.
At the core of every network are components linked together and communicating with one another. Each network comprises at least two devices, as connectivity requires a minimum of two endpoints. However, networks can scale exponentially, potentially connecting billions of devices globally, such as the Internet.
The Significance of Networks
Networks facilitate communication between computers and access to vast amounts of information, such as the Internet. For example, they enable accessing weather data and controlling devices remotely.
In the digital landscape, networks serve as vital conduits, enabling seamless communication and access to a wealth of information.
However, this connectivity also introduces inherent vulnerabilities. Networks face constant threats, ranging from cyberattacks to data breaches.
As a result, network security has become a paramount concern. Cybersecurity professionals advocate for proactive measures such as access controls, encryption, and employee awareness to mitigate risks. With the proliferation of IoT devices, the attack surface has expanded, necessitating a multifaceted approach to defense.
Basics of the Internet: Biggest Network in World
There is a network that we use frequently today, we call it the internet. You are accessing the article you are currently reading from a device via the internet.
Internet is formed by connecting small networks (private networks) that are independent of each other with the help of the public network.

As seen in the picture above, we have 3 hidden networks (can be on different devices instead of computers), while these networks are private in themselves, these private networks are connected to each other with the internet.
If you prefer the private network to share information, you can share information only with devices in the private network, if you prefer the public network, you can transfer data with anyone connected to that network.
Unveiling Network Devices: Navigating through IP and MAC Addresses
Discovering devices on a network is essential for managing and securing infrastructure. Two primary methods are used: IP addresses, which facilitate communication, and MAC addresses, unique hardware identifiers.
Additionally, leveraging these methods, administrators can efficiently monitor, troubleshoot, and enforce security measures across the network.
1. IP Address
The IP address identifies the computer on the network for a short time, unlike MAC (media access protocol), the IP address can be changed easily.
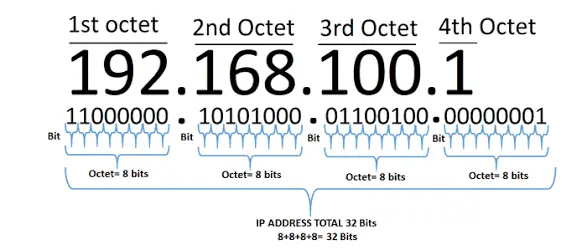
An IP address is a set of numbers that are divided into four octets, for example, the IP address 192.168.1.1 can be given.
The IP addresses can be changed manually or, automatically with VPN, but two computers with the same IP cannot exist on the same network.
We have two IP address types, these are public and private. The public address is used to identify the device on the Internet.
A private IP address serves as the gateway for local connections between devices within a network. Unlike your public-facing IP address on the Internet, your private network IP address operates within a closed ecosystem.
This distinct allocation ensures that internal communications remain secure and isolated from external networks, fostering efficient data exchange and resource sharing among interconnected devices.
Like the diagram above, every device in the private network uses private IP to communicate with each other, but every device connects to the internet with the same public IP.
Public IP addresses are provided to you by the Internet Service Provider (ISP) for a monthly fee.
2. Mac Address
A MAC address is a unique identifier assigned to network devices like computers, printers, and routers. It comprises 12 hexadecimal digits, with the first six representing the manufacturer’s unique identifier (OUI), and the remaining six as the device’s serial number.
This permanent label distinguishes devices on a network, aiding communication. Unlike IP addresses, which can change, a MAC address remains constant, crucial for network management, security, and troubleshooting.
MAC Spoofing
Some firewalls use MAC addresses to identify the user, which can lead to an attack called MAC address spoofing.
Attackers can masquerade as other users by altering their MAC address, potentially intercepting messages intended for someone else.
To change a MAC address, users can use specialized software or OS commands to modify network adapter settings, disguising their device’s identity and bypassing MAC address verification security measures.
Examples include MACchanger for Linux or Technitium MAC Address Changer for Windows.
Ping and ICMP Packets
A ping is a tool used to determine the performance of the connection between devices. It offers the ping command ready in operating systems terminals.
Ping uses ICMP (Internet Control Message Protocol) packets. The time taken for ICMP packets traveling between devices is measured by ping.
ping 192.168.1.1With the help of the command above, you can ping the desired destination (you can modify the packets with different settings).
What is Ping of Death?
A Ping of Death (PoD) attack occurs when an attacker sends oversized or malformed packets using the ping command, destabilizing the target system.
These large packets can cause buffer overflow when assembled, damaging the machine.
Understanding DDoS Attacks
These attacks entail flooding a target with an overwhelming volume of packets from numerous sources, effectvely saturating its resources and rendering it inaccessible to legitimate users.
Unlike traditional cyber intrusions aimed at infiltration, DDoS assaults are executed solely to cripple or disrupt the target’s operations.
By inundating the target with an excessive influx of traffic, DDoS attacks can inflict severe damage, not only compromising the target’s online presence but also potentially causing harm to its hardware infrastructure.
Check out more articles about cyber security.